Detect web-app hackers
LONG BEFORE THEY ATTACK
by profılıng theır recon on your app!
Introducing “WEB-APP Recon detectıon”
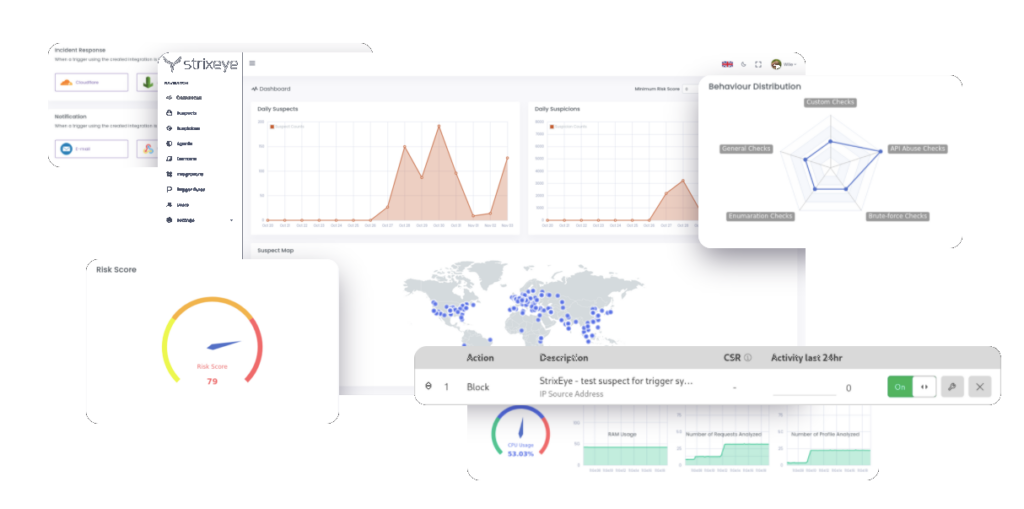
StrixEye analyzes all visitors of your web-app (monolith websites & APIs), profile suspicious flows of unsuspicious requests, classify suspects and conduct risk-scoring. This architecture lets you gain insights from potential hackers’ point of view. “Web-app recon detection” introduces a methodology which enables predicting business-logic & 0-day attacks.
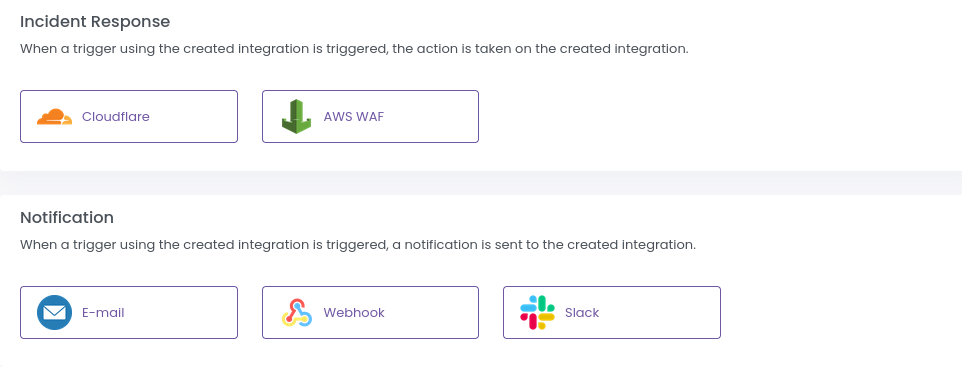
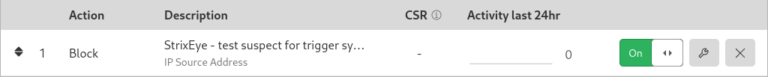
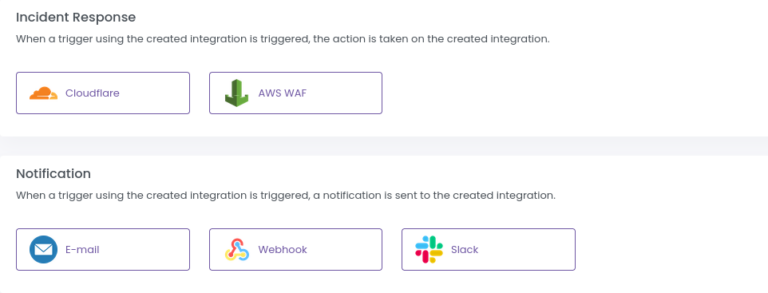
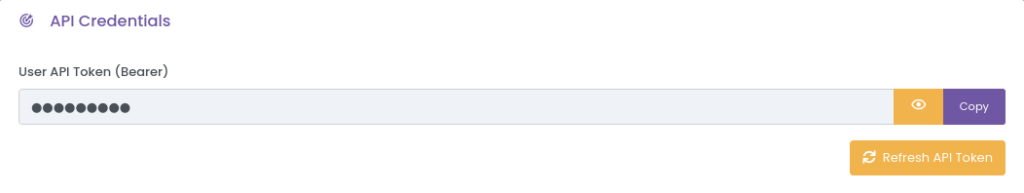
StrixEye has a built-in WAF and can be integrated to several technologies including team management platforms, WAFs, firewalls, SIEMs & SOARs. These capabilities enable notifying security teams, challenging suspicious visitors, blocking high-risk profiles based on their risk-scores.
Steps of StrixEye’s Operating Principles

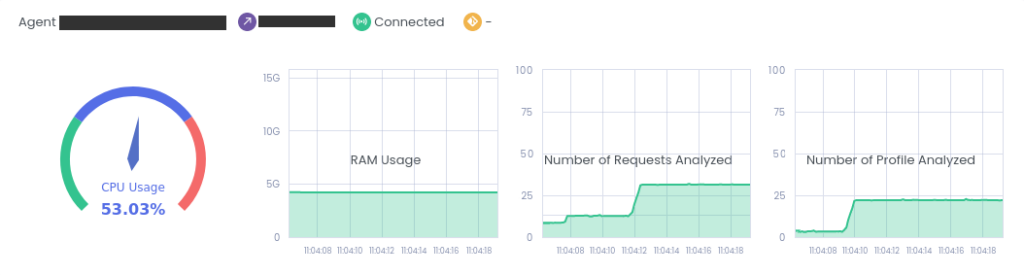
Analysis
Analyzes every HTTP/HTTPS request chain of your each visitor using smart flow-checks.
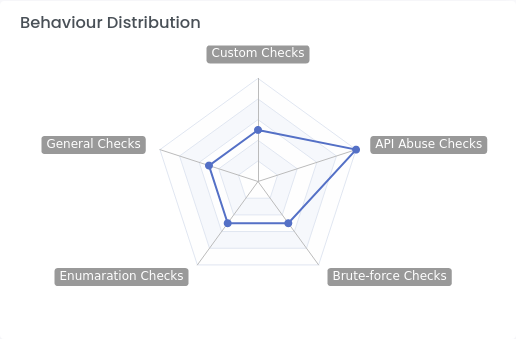
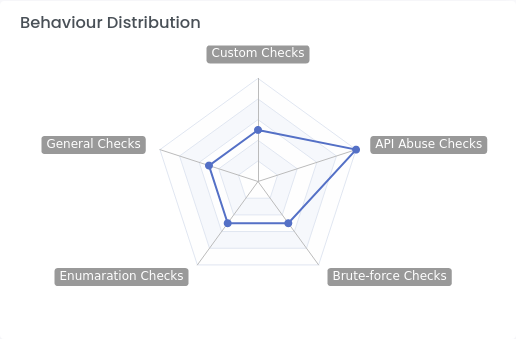
Classification & Profiling
Classifies suspicious users, and profiles their behavior step-by-step.

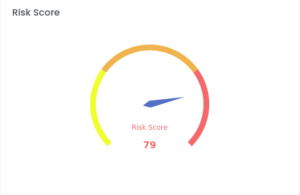
Risk Scoring
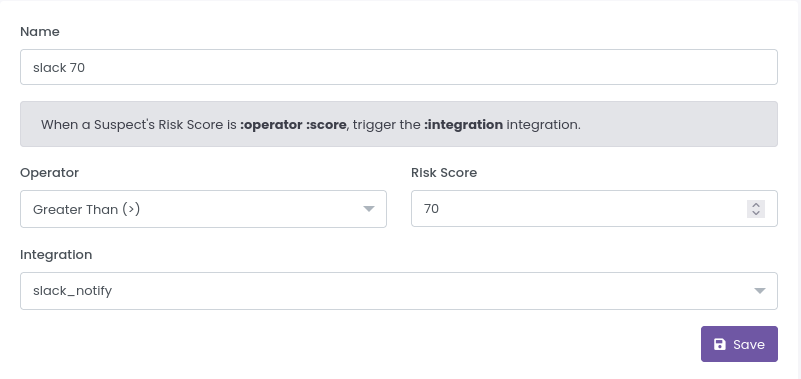
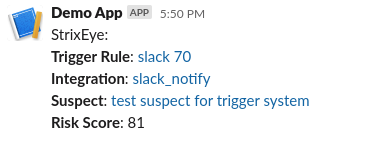
Conducts risk-scoring based on the suspects’ behavior.

Notification
Notifies your security team when a suspect’s risk-score reaches your pre-defined levels.

Protection
Allows generating automated rules for your WAFs and firewalls to protect your web-apps.
Discovery
Helps you discover vulnerabilities, which cause business-logic & 0-day attacks, while being tampered, long before being exploited.
Discovery
Helps you discover vulnerabilities, which cause business-logic & 0-day attacks, while being tampered, long before being exploited.

Protection
Allows generating automated rules for your WAFs and firewalls to protect your web-apps.

Analysis
Analyzes every HTTP/HTTPS request chain of your each visitor using smart flow-checks.
Classification & Profiling
Classifies suspicious users, and profiles their behavior step-by-step.

Risk Scoring
Conducts risk-scoring based on the suspects’ behavior.

Notification
Notifies your security team when a suspect’s risk-score reaches your pre-defined levels.
Integrations
StrixEye has integration capabilities with most popular WAFs, firewalls and team management platforms in order to trigger your pre-defined rules and ensure your security.







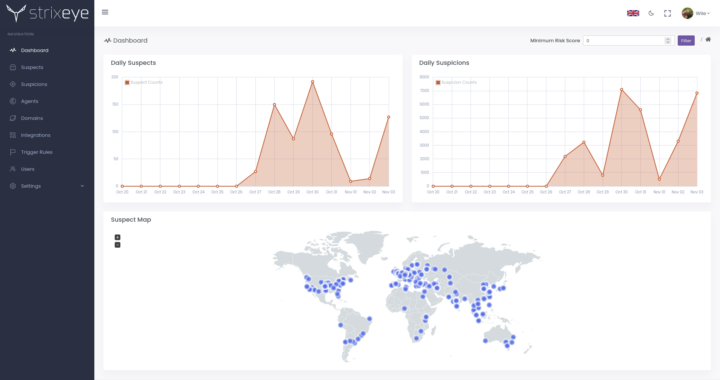
Keep Track With Our Dashboard
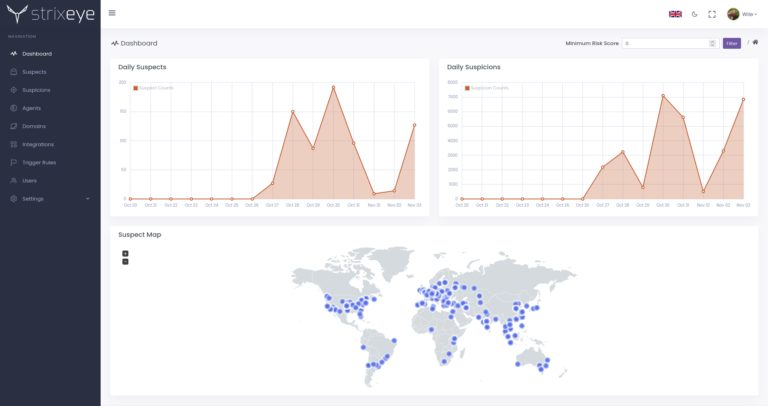
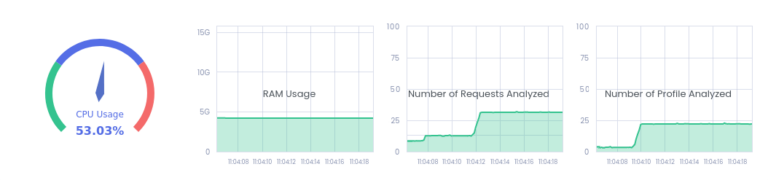
Keep Track With Our Dashboard